With the increased global penetration of mobile phones, there is a significant growth in the need for cybersecurity. Global improvements in the Internet and mobile connectivity, as well as technological breakthroughs, are driving the adoption of intelligent gadgets among businesses and consumers. Simultaneously, enterprises are rapidly adopting cloud services and other networking innovations.
This also means that businesses are becoming exposed to numerous cyber-attacks.
Growing cyber threats contributed to the need for cybersecurity certifications, particularly code signing certificates. Code signing certificates offer end users security and confidence in the code/software programs generated by IT firms.
Moreover, instilling faith in your consumers that the program they are installing is secure is essential. This is also why you must get a code signing certification.
What is the need for code signing?
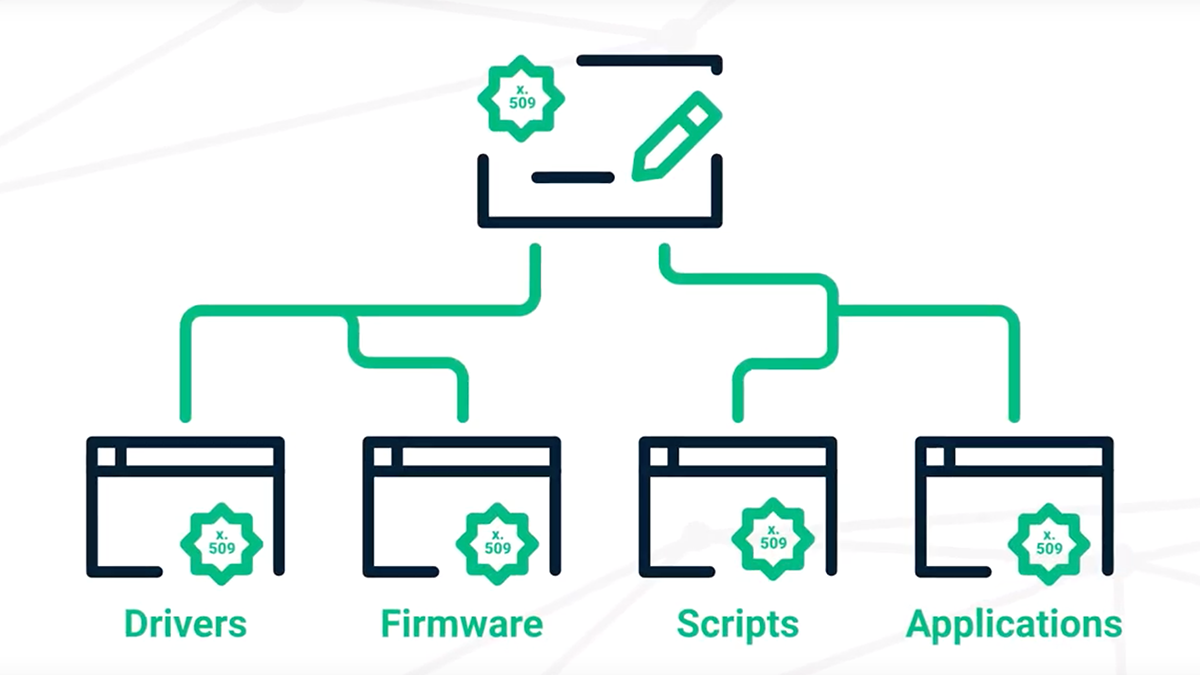
Code signing is the procedure by which a software programmer signs programs and executables before making them available to the general public. This certificate verifies that the downloaded program is obtained straight from the publisher. It increases the number of software installations and improves the software developer’s brand reputation. Furthermore, the certificate validates the publisher’s identity and code integrity. It also allows consumers to accept upgrades because all leading platforms and operating systems support code signing.
Businesses are implementing numerous reliable code signing tools to improve end-user security and experience. At the same time, these tools allow them to secure their information and improve trust in their services.
Why should you utilize code signing solutions?
Code signing is among the most secure processes for ensuring the integrity of software and code. This feature makes code signing so desirable among developers and tech companies.
Let us examine some critical advantages of code signing to secure your software.
- Code security is safeguarded
Completing code signing allows you to use the platform to safeguard the company’s unique code and software programs.
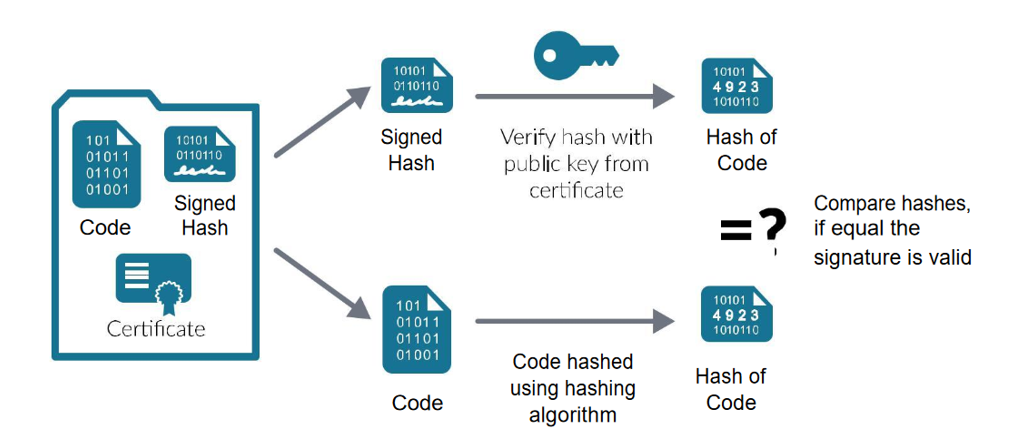
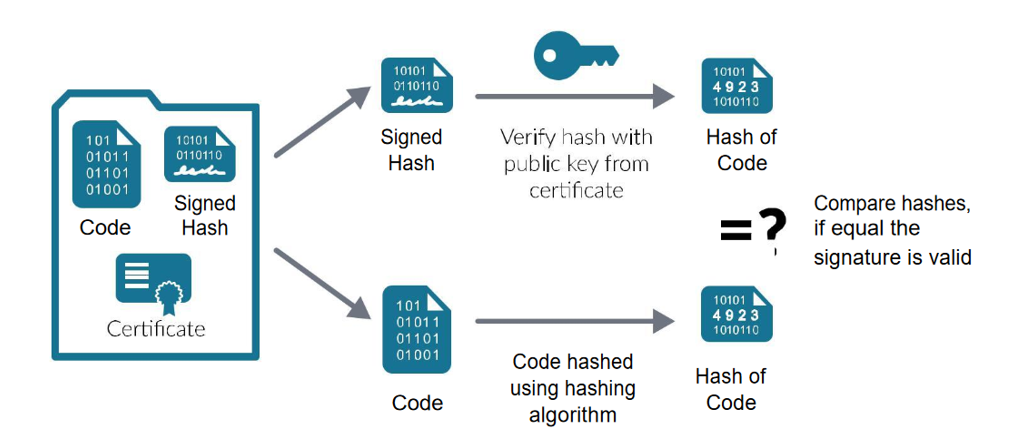
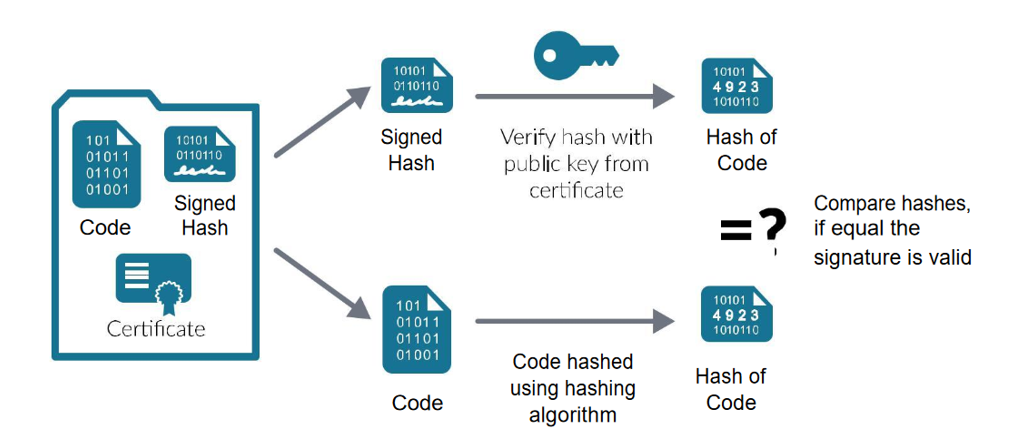
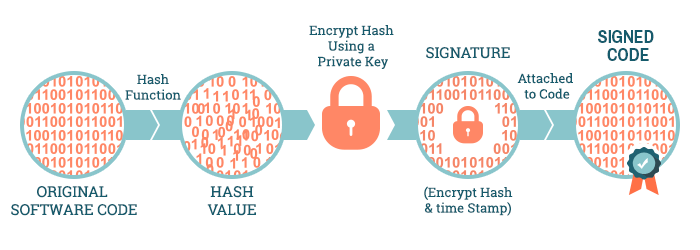
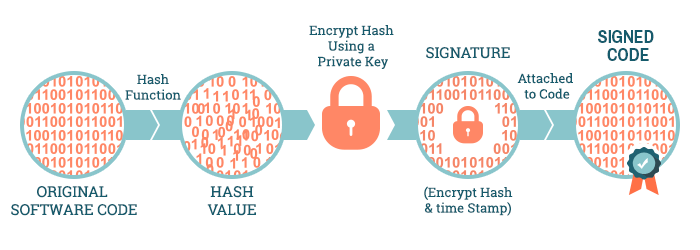
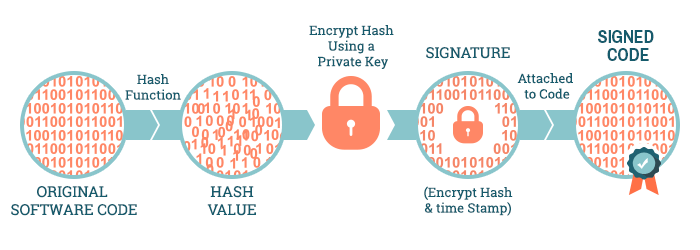
Code signing authenticates the code or software program’s authenticity by employing a hash function. The code integrity is maintained if the hash utilized to sign the app fits the hash on a downloadable app. If the hash does not fit, users receive a security alert, and the code does not execute. Code signing certifications provide an optional timestamp to prolong the validity of your digital signatures.
Since experts can verify the legitimacy of the code signing certification at the digital signature time, your software will remain valid even if the certificate expires.
- Timestamping
Time stamping is an alternative measure in the code signing procedure that enables software to determine whether a code signing sign is genuine even after a code signing certification has expired.
- Simplified code security
When you use API integration to combine code programs with code signing sites, experts will make code signing simple to maintain and connect with your code. Simplified security allows you to get to market quicker while safeguarding the security of the code and lowering security warnings.
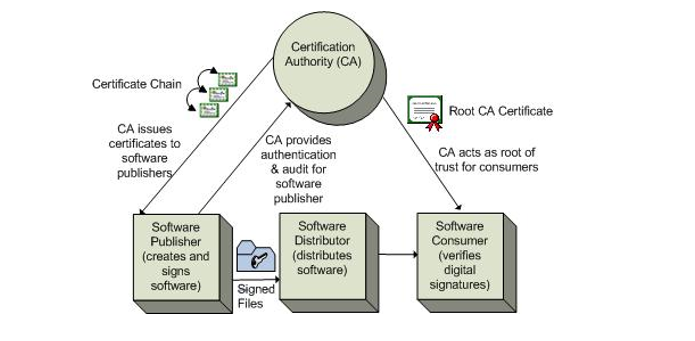
Organizations can reduce security warnings by leveraging certificates from respected Certificate Authorities (CA), generating and establishing confidence in end-users.
You will deploy root certificates from trusted and reputable certificate authorities on the client host computers. As a result, it is always recommended to use conventional code signing services. When you utilize code signing, your software is immediately accepted, and no security warnings are issued. That will allow for the program or code to be downloaded seamlessly. The end user will find it easier to use with fewer security alerts.
- Increase distribution and revenue
The spread of malware and developing consumer apps for desktop and mobile platforms make code signing more critical than ever.
Software and mobile network providers frequently request code signing from a trusted Certificate Authority before accepting code for deployment, improving security and reliability.
- Ensure a safe and secure consumer experience
Digital certificates assist in the creation of a unified user experience that reduces security alerts and installation errors while increasing code adoption and revenue potential. Signing the code assures that it has not been changed and is genuine.
Besides, signing it using a code signing certificate demonstrates that you are recognized by the industry leader in code signing safety and contributes to a safe and secure environment for you and your clients.
- Identify modified files
When you electronically sign your codes, you can readily spot easily changed, interfered with, or mimicked files. You can ensure the authority of a code signing certification even after it has expired. This one is because of the timestamping capabilities of the same.
Code signing certificate categories
- Standard Validation certificates
This is the most common code signing certificate and entails the CA performing necessary approvals on the publisher or programmer. To obtain a standard code signing certificate, software developers must meet specific basic standards like minimum key length and digital signature stamping.
- Extended Validation (EV) certifications
EV code signing credentials require the CA to validate and vet the software developer and are typically given on a hardware token for added security.
Conclusion
More people are installing software to help them with their daily tasks. However, they are frequently concerned about whether they are installing actual software. Moreover, there have been reports of customers downloading malicious malware that harmed their PCs. Hence, code signing is essential for protecting both users and developers. From a programmer’s standpoint, code signing safeguards the code and improves your reputation. That eventually leads to higher download numbers. If you are a consumer, you must rely on obtaining signed software. Additionally, secure technology can help organizations with sensitive information and copyrighted programs.